Information Security
- Editor's letterIs your identity management up to the task?
- Cover storyNew tech steers identity and access management evolution
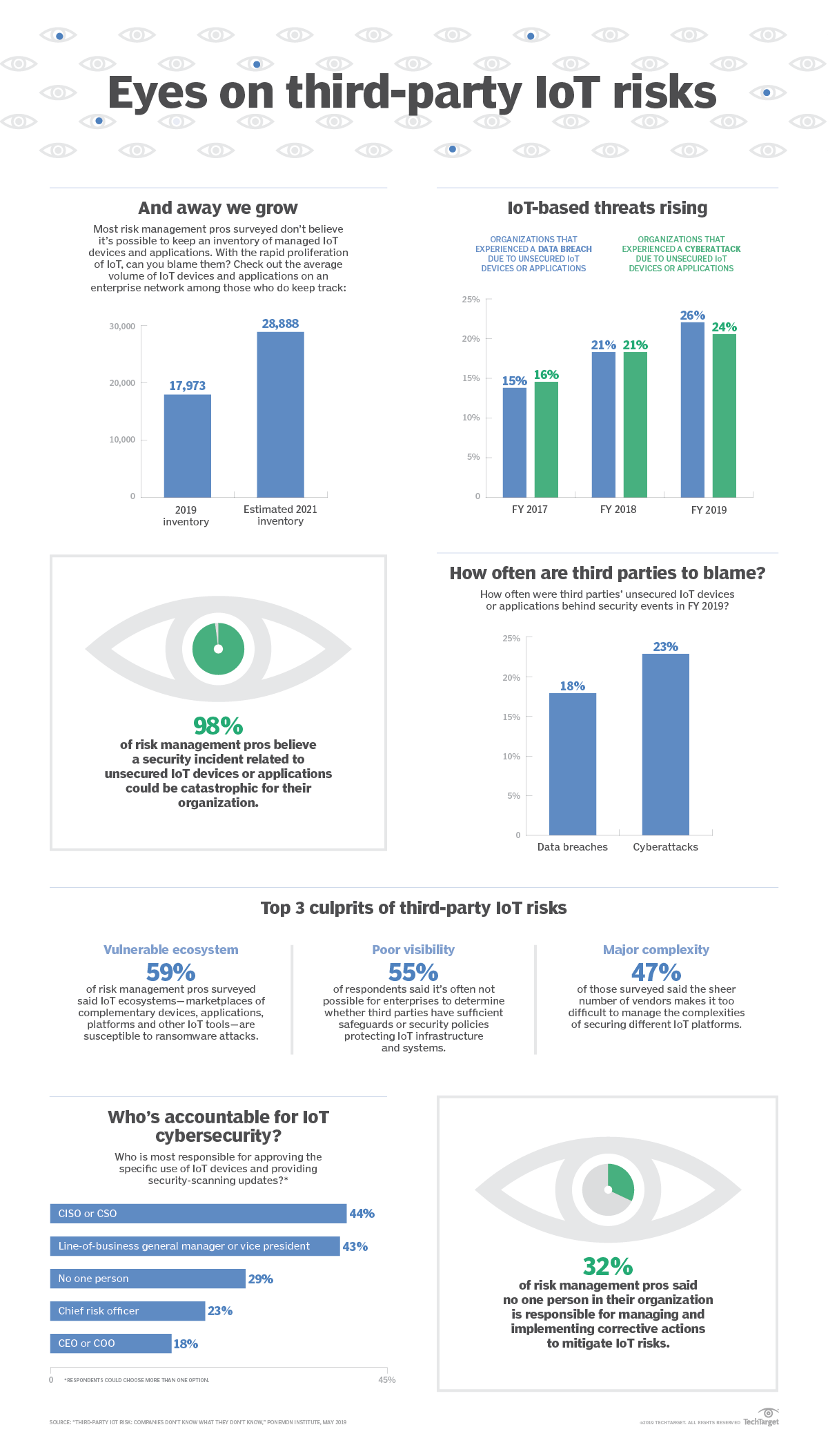
- InfographicIoT cybersecurity: Do third parties leave you exposed?
- FeatureFitting cybersecurity frameworks into your security strategy
- ColumnFor board of directors, cybersecurity literacy is essential
- ColumnThe must-have skills for cybersecurity aren't what you think
IoT cybersecurity: Do third parties leave you exposed?
IoT's vast vendor landscape drives innovation, but working with so many third parties also comes with baggage in the form of third-party cybersecurity issues.In some ways, security is all about perspective. It wasn't that long ago that BYOD felt like a daunting challenge for information security and risk management professionals. But, now, a couple hundred smartphones and iPads can seem like child's play compared to IoT cybersecurity, which involves protecting everything from connected cars to networked sensors to smart locks and control systems.
Part of what makes IoT cybersecurity so complex is its reliance on a vast ecosystem of third-party providers. While many of these companies aspire to deliver a unified approach to security, the reality is that it can be incredibly challenging for enterprise IT teams to get different devices, platforms and systems to play nicely together.
A May 2019 report by Ponemon Institute revealed that, even among IoT-savvy organizations, corporate risk management pros are largely aware of third-party cybersecurity vulnerabilities but still have a ways to go in mitigating such IoT cybersecurity gaps.