What is SSH (Secure Shell) and How Does It Work?
SSH (Secure Shell or Secure Socket Shell) is a network protocol that gives users -- particularly systems administrators -- a secure way to access a computer over an unsecured network.
SSH also refers to the suite of utilities that implement the SSH protocol. Secure Shell provides strong password authentication and public key authentication, as well as encrypted data communications between two computers connecting over an open network, such as the internet. SSH is important for maintaining the security of systems, as the protocol acts as a secure way to provide access and management of networked systems.
In addition to providing strong encryption, SSH is widely used by network administrators to manage systems and applications remotely, enabling them to log in to another computer over a network, execute commands and move files from one computer to another.
SSH refers to both the cryptographic network protocol and to the suite of utilities that implement that protocol. SSH uses the client-server model, connecting a Secure Shell client application, which is the end where the session is displayed, with an SSH server, which is the end where the session runs. SSH implementations often include support for application protocols used for terminal emulation or file transfers.
SSH can also be used to create secure tunnels for other application protocols -- for example, to securely run X Window System graphical sessions remotely. An SSH server, by default, listens on the standard TCP port 22.
How does SSH work?
Secure Shell was created to replace insecure terminal emulation or login programs, such as Telnet, remote login (rlogin) and remote shell (rsh). SSH enables the same functions -- logging in to and running terminal sessions on remote systems. SSH also replaces file transfer programs, such as File Transfer Protocol (FTP) and remote copy (rcp).
SSH runs on the TCP/IP protocol suite in a client-server architecture. SSH provides encryption and authentication using public key cryptography. The most basic use of SSH is to connect to a remote host for a terminal session. The form of that command, as an example, looks like the following:
ssh [email protected]
This command causes the client to attempt to connect to the server named server.example.com, using the user ID UserName. If this is the first time negotiating a connection between the local host and the server, the user is prompted as follows with the remote host's public key fingerprint to connect, despite having no prior connection:
The authenticity of host 'sample.ssh.com' cannot be established.
DSA key fingerprint is 01:23:45:67:89:ab:cd:ef:ff:fe:dc:ba:98:76:54:32:10.
Are you sure you want to continue connecting (yes/no)?
Answering yes to the prompt causes the session to continue, and the host key is stored in the local system's known_hosts file. This is a hidden file stored by default in a hidden directory, called /.ssh/known_hosts, in the user's home directory. Once the host key has been stored in the known_hosts file, the client system can connect directly to that server again without the need for any approvals; the host key authenticates the connection.
What is SSH used for?
Present in all data centers, SSH ships by default with every Unix, Linux and Mac server. SSH connections are used to secure many different types of communications between a local machine and a remote host, including secure remote access to resources, remote execution of commands, delivery of software patches, updates and other administrative or management tasks.
In addition to creating a secure channel between local and remote computers, SSH is used to manage routers, server hardware, virtualization platforms and operating systems (OSes), as well as inside systems management and file transfer applications.
Secure Shell is used to connect to servers, make changes, perform uploads and exit, either using tools or directly through the terminal. SSH keys can be used to automate access to servers and are often used in scripts, backup systems and configuration management tools.
Designed to be convenient and work across organizational boundaries, SSH keys provide single sign-on (SSO) so that users can move between their accounts without having to type a password each time.
SSH can also be used to create secure tunnels for other application protocols. For example, secure tunnels can be used for local, remote and dynamic port forwarding. While playing pivotal roles in identity and access management, SSH does more than authenticate over an encrypted connection. All SSH traffic is encrypted. Whether users are transferring a file, browsing the web or running a command, their actions are private.
While it's possible to use SSH with an ordinary user ID and password as credentials, SSH relies more often on key-based authentication using public key pairs to authenticate hosts to each other. Individual users must still employ their user ID and password -- or other user authentication methods -- to connect to the remote host itself, but the local machine and the remote machine authenticate separately from each other. This is accomplished by generating a unique public key pair for each host in the communication. A single session requires two public key pairs: one public key pair to authenticate the remote machine to the local machine and a second public key pair to authenticate the local machine to the remote machine.
SSH is also used to manage and configure firewalls or other security applications, ensuring secure administrative configuration changes and access.
Secure Shell capabilities
SSH enables the following functions:
- Secure remote access to SSH-enabled network systems or devices for users, as well as automated processes.
- Secure and interactive file transfer sessions.
- Automated and secured file transfers.
- Secure issuance of commands on remote devices or systems.
- Secure management of network infrastructure components.
- Authentication and host-based authentication.
- Remote execution of commands.
- Port forwarding.
- Session and key management.
SSH can be used interactively to enable terminal sessions and should be used instead of the less secure Telnet program. SSH is also commonly used in scripts and other software to enable programs and systems to remotely and securely access data and other resources.
Secure Shell security issues
Enterprises using SSH should consider finding ways to manage host keys stored on client systems. These keys can accumulate over time, especially for IT staff who need to access remote hosts for management purposes.
Because the data stored in an SSH known_hosts file can be used to gain authenticated access to remote systems, organizations should be aware of their existence and have a standard process for retaining control over them, even after a system is taken out of commission, as the hard drives might have this data stored in plaintext.
Developers should be careful when incorporating SSH commands or functions in a script or other type of program. While it's possible to issue an SSH command that includes a user ID and password to authenticate the user of the local machine to an account on the remote host, doing so can expose the credentials to an attacker who has access to the source code.
Shellshock, a security hole in the Bourne again shell (Bash) command processor, can be executed over SSH but is a vulnerability in Bash, not in SSH.
The biggest threat to SSH is poor key management. Without the proper centralized creation, rotation and removal of SSH keys, organizations can lose control over who has access to which resources and when, particularly when SSH is used in automated application-to-application processes.
SSH vs. Telnet
Telnet was one of the first internet application protocols. It's used to initiate and maintain a terminal emulation session on a remote host.
SSH and Telnet are functionally similar, with the primary difference being that the SSH protocol uses public key cryptography to authenticate endpoints when setting up a terminal session, as well as for encrypting session commands and output.
SSH encrypts all data transmitted between the client and server, which includes passwords and commands. Telnet, however, transmits all data in plaintext, making it much more vulnerable. SSH also supports multiple authentication methods, including public key, password and multifactor authentication, while Telnet typically just uses username and password authentication. While Telnet is primarily used for terminal emulation, SSH can be used for terminal emulation -- similar to the rlogin command -- as well as for issuing commands remotely as with rsh, transferring files using SSH FTP (SFTP) and tunneling other applications.
SSH vs. SSL/TLS
The Transport Layer Security (TLS) protocol, which updates the Secure Sockets Layer (SSL) protocol, was designed to provide security for network transmissions at the transport layer. The SSH protocol also operates at or just above the transport layer, but there are important differences between the two protocols.
While both rely on public or private key pairs to authenticate hosts, only the server is authenticated with a key pair under TLS. SSH uses a separate key pair to authenticate each connection: one key pair for a connection from a local machine to a remote machine and a second key pair to authenticate the connection from the remote machine to the local machine.
Another difference between SSH and TLS is that TLS can be encrypted without requiring authentication and can authenticate without encryption. SSH encrypts and authenticates all connections.
SSH provides IT and information security professionals with a secure mechanism to manage SSH clients remotely. Rather than requiring password authentication to initialize a connection between an SSH client and server, SSH authenticates the devices themselves. This enables IT staff to connect with remote systems and modify SSH configurations, including adding or removing host key pairs in the known_hosts file.
SSH implementations
SSH is an open protocol. It has been implemented for most computing platforms. The open source OpenSSH implementation is mostly found on Linux, Unix and other OSes based on Berkeley Software Distribution (BSD), including Apple's macOS.
OpenSSH was ported to run in Windows PowerShell starting in 2015. In 2018, optional OpenSSH support was added to Windows 10. While SSH is directly accessible by default in most Unix-like OSes, Microsoft's ported version of OpenSSH must be explicitly enabled in the Windows Settings app.
PuTTY is another open source implementation of SSH. While it's currently available for Windows, macOS, Unix and BSD, PuTTY was originally written to run on Windows. It has long been one of the top options for using SSH on a Windows system.
Most implementations of the SSH suite comprise the following three utilities:
- secure login (slogin).
- ssh.
- secure copy (scp).
These are secure versions of the earlier insecure Unix utilities rlogin, rsh and rcp.
SSH uses public key cryptography to authenticate the remote computer and enable the remote computer to authenticate the user, if necessary.
There are currently dozens of SSH implementations available for various platforms and under a variety of open source and proprietary licenses.
SSH commands
While there are graphical implementations of SSH, the program is usually invoked at the command line or executed as part of a script. Running the ssh command on its own with no arguments, such as a destination host or user ID, returns a list of SSH command parameters and options.
The most basic form of SSH command is to invoke the program and the destination host name or IP address as follows:
ssh server.example.org
This connects to the destination, server.example.org. The destination host responds by prompting for a password for the user ID of the account under which the client is running. In other words, if the user ID in use is jsmith, then the remote host asks for a password associated with the account jsmith on the remote host.
In many cases, the user ID for the remote host is different, in which case the command should be issued with the remote host user ID as follows:
ssh [email protected]
SSH can also be used from the command line to issue a single command on the remote host and then exit, for example:
ssh example.org ls
This executes the Unix ls command, which lists all contents of the current directory on the remote host. While this example is trivial, it demonstrates that SSH can be used to execute more interesting commands on a remote host. For example, a command can be crafted that initializes a server instance that gives a remote machine access to a single file -- or other resource -- and then terminates the server after the file is accessed by the specified remote host.
In addition to the ssh executable, SSH has other executable commands used at the command line for additional functions, including the following:
- sshd initiates the SSH server, which waits for incoming SSH connection requests and enables authorized systems to connect to the local host.
- ssh-keygen is a program that creates a new authentication key pair for SSH, which can be used to automate logins, implement SSO and authenticate hosts.
- ssh-copy-id is a program used to copy, install and configure an SSH key on a server to automate passwordless logins and SSO.
- ssh-agent is a helper program that tracks identity keys and their passphrases -- from which SSH derives an encryption key -- and enables the user to use the identity keys to log in to different servers without the need to reenter passwords or passphrases.
- ssh-add is used to add a key to the SSH authentication agent and is used with ssh-agent to implement SSO using SSH.
- scp is a program used for copying files from one computer to another and is an SSH-secured version of rcp.
- sftp is a program used to copy files from one computer to another and is an SSH-secured version the original FTP. SFTP has become the preferred mechanism for file sharing over the internet, replacing both FTP and FTP Secure, which is a protocol for using FTP over an SSL/TLS tunnel.
- cd is used to change the directories on a remote server.
- pwd is used to display the current working directories on a remote server.
What is SSH tunneling?
SSH tunneling, also known as SSH port forwarding, is a technique that lets a user open a secure tunnel between a local host and a remote host to transmit data. SSH tunneling is typically used to access remote services securely, securely connect to distributed systems and bypass restrictions.
SSH port forwarding redirects network traffic to a particular port or IP address so that a remote host is made directly accessible by applications on the local host. The destination can be on the remote SSH server, or that server might be configured to forward to yet another remote host.
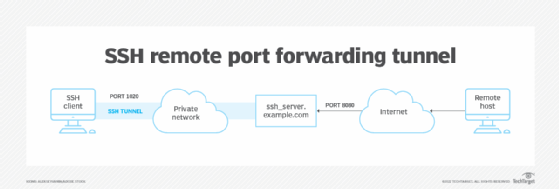
There are multiple types of forwarding supported by SSH tunneling, including local port forwarding, remote port forwarding and dynamic port forwarding.
Remote port forwarding enables remote services to be securely accessed from the client side through an SSH tunnel. Local port forwarding, on the other hand, enables client-side applications to securely access services running on the SSH server. Dynamic port forwarding provides a more flexible way to secure and route traffic for multiple applications using one SSH connection. SSH tunnels are powerful tools for IT administrators, as well as malicious actors, because they can transit an enterprise firewall undetected. As a result, there are tools available to prevent unauthorized use of SSH tunnels through a corporate firewall.
The history of SSH
The first version of SSH appeared in 1995 and was designed by Tatu Ylönen, who was, at the time, a researcher at Helsinki University of Technology and later started SSH Communications Security Corp., a cybersecurity vendor based in Finland.
Over time, various flaws were found in SSH1, leading to this version being deprecated and considered unsafe to use.
Secure Shell 2.0 or SSH2, the current version of the Secure Shell protocol, was adopted as a standards-track specification by the Internet Engineering Task Force in 2006. SSH2 isn't compatible with SSH1 and uses Diffie-Hellman key exchange and a stronger integrity check that uses message authentication codes to improve security.
SSH clients and servers can use several encryption methods, the most widely used being Advanced Encryption Standard and Blowfish.
Since its development, several SSH2 vulnerabilities have been found. In 2008, a theoretical vulnerability was found for all SSH versions that enabled the recovery of up to 32 bits of plaintext from a block of encrypted ciphertext.
Likewise, information leaked by Edward Snowden in 2013 suggested the National Security Agency might be able to decrypt some SSH traffic.
A man-in-the-middle attack, known as Terrapin, was discovered in 2023. The attack was caused by a vulnerability related to the cipher block chaining (CBC) decryption oracle in OpenSSH. The vulnerability could enable an attacker to recover plaintext from encrypted SSH sessions through exploiting weaknesses found in the CBC decryption process. Patches and updates were later released to mitigate the attack.
Despite these vulnerabilities, SSH2 is still generally considered secure when it's implemented correctly and has current configurations.
To ensure security, it's important to use the latest and most up-to-date version of SSH. Learn more about how SSH1 and SSH2 compare.





