Cloud migration security challenges and best practices
Cloud migration can seem daunting to security teams. Following these essential practices can help them move infrastructure and applications to the cloud safely and securely.
As organizations plan to move workloads and applications into the cloud, they encounter a fundamental problem. The security controls and practices they've built for their on-premises environments aren't quite what they'll need in the cloud, where everything is software-based and deeply integrated.
Cloud migration consists of moving existing assets, typically applications and server workloads, into a cloud environment. In some cases, these migrations are relatively transparent and straightforward -- for example, moving a Microsoft Windows file share from an on-premises virtual machine to a cloud-based Windows file share instance. Other cloud migrations are much more complex and can vary significantly due in part to the use of more cloud-native services, APIs, controls and components not seen in the on-premises world.
How does cloud migration security work?
The cloud presents new opportunities for enterprises but also comes with new risks and other issues as well as strategies to mitigate them. Organizations should approach the security aspects of a cloud migration carefully, from fundamentals of access control and governance to API integrations and continuous monitoring.
They should first examine their existing security requirements and policies as well as controls and processes for regulatory compliance. It's also helpful to ask the following questions:
- Are we migrating systems and applications 100% or only changing them in certain ways?
- Do we need to use traditional virtual machine workloads or can we move to more cloud-native workloads like containers or serverless options?
- Which security controls will stay the same and which ones are changing?
- Is the workload or application more exposed as a result of the migration?
- What risk mitigation controls are available in the cloud environment?
Security teams involved in a cloud migration will ideally also perform some type of threat modeling exercise to better understand the business case and technology use cases for the workloads being moved, the cloud destination and potential increased risks that need to be mitigated during the migration.
Why security is important during cloud migration
Security is a critical consideration in cloud migration due to the potentially sensitive nature of the data, systems and applications involved. Without a solid security strategy, organizations risk exposing their assets to threats that can lead to data breaches, operational disruptions and compliance failure. Here's more about why security is essential during cloud migration:
- Protecting sensitive data. Data in transit and at rest during migration is vulnerable to interception and unauthorized access, and security teams should use encryption (transport layer security for data in transit, Advanced Encryption Standard for data at rest) and ensure strict access controls for all cloud data storage and transit.
- Ensuring compliance with regulations. Failing to secure cloud environments and data can result in compliance and audit issues for industry regulations, such as GDPR, HIPAA and Payment Card Industry Data Security Standard. Be sure to map compliance requirements to migration processes and implement appropriate safeguards.
- Mitigating downtime and operational disruptions. Security incidents during migration can lead to system outages and business interruptions. Conduct risk assessments and implement real-time monitoring to detect and mitigate issues.
- Avoiding shadow IT risks. Unmonitored or unauthorized cloud instances and services might emerge during the migration, expanding the attack surface. To avoid this, maintain an inventory of assets and employ strict governance policies.
- Establishing secure identity and access management (IAM). Unauthorized access to cloud resources during migration can lead to data breaches. Implement strong IAM policies, such as multifactor authentication and role-based access control.
- Maintaining visibility and control. Lack of visibility into data movement and access during migration increases the risk of undetected threats. Use network monitoring tools and other tools and services for real-time monitoring and logging to maintain control and traceability.
Cloud migration security considerations
Important cloud security considerations are numerous, but the following should be the top priorities:
- Regulatory and compliance requirements. Any cloud environment you migrate to must meet necessary regulations and compliance requirements. All major cloud service providers offer a range of compliance and audit attestations related to the capabilities and controls they maintain under the shared responsibility model. However, organizations must still make sure they meet privacy requirements on their end of the shared responsibility. For example, they might need specialized cloud security controls and services to meet stringent industry requirements, such as those for finance, healthcare and government agencies.
- Cloud control plane visibility. The cloud control plane provides a set of controls and settings and enables various kinds of functionality, such as logging enablement and administrative access. Large, complex environments, such as AWS and Microsoft Azure, can have an overwhelming number of settings to enable and monitor. Organizations should use industry best practices, such as applying the Center for Internet Security benchmarks to initially configure and secure cloud accounts and subscriptions, and carefully monitor for changes and risky configuration settings.
- Privileged access controls. A cloud migration introduces new types of privileged users, such as cloud architects, site reliability engineers and DevOps engineers. Plan to implement strong privilege oversight when moving to most cloud provider environments.
- Automation and APIs. Organizations must design security controls with some degree of automation to adapt and scale throughout a cloud migration and keep up with the pace of ongoing cloud operations. This is most often accomplished through extensive use of cloud provider APIs, as well as specialized tools and services that can help streamline and integrate security automation for desired use cases.
Top security challenges faced during cloud migration
Alongside the plethora of cloud security considerations during cloud migrations, security teams should prepare to encounter and mitigate an array of challenges along the way, including the following:
- Lack of skills and knowledge. Many DevOps and cloud engineering teams take things into their own hands due to a lack of understanding of cloud technology and security.
- Data exposure. Large cloud service environments contain a wide variety of data storage and processing services. It's easy to accidentally expose data through poorly configured access controls, encryption and other data protection measures.
- Lack of visibility and monitoring. Cloud migrations introduce a much more dynamic pace of change into day-to-day operations. Security teams often scramble to understand what is going on in cloud environments, especially when dealing with a multi-cloud environment.
- Poor IAM. It is a challenge to identify appropriate least-privilege roles and identity policies, particularly in large, multi-cloud scenarios that involve numerous types of use cases and different identity policy engines for each provider. Weak or improperly applied identity policies and permissions are a vulnerable target for attackers in the cloud.
- Misconfigured control plane settings. In addition to IAM, the cloud control plane handles various configuration settings that, if improperly managed, could lead to exposure or increased threat surface. These could include administrative console access, weak authentication requirements, porous network access controls and exposed APIs.
Best practices to mitigate cloud migration security risks
Organizations can take many steps to successfully prepare for and mitigate cloud migration security challenges.
The most important first step in a cloud migration plan is to establish proper cloud governance. For day-to-day cloud engineering, oversight and administration, including change management, design a governance model with the following breakdown of teams:
- Central DevOps and cloud engineering. This team manages the DevOps pipeline -- code, builds, validation and deployment. Ideally, it integrates security tools, such as static code assessment and dynamic web scanning, throughout the pipeline through automation. It's a multidisciplinary team that includes developers and infrastructure specialists who have adapted their skills to infrastructure as code (IaC) and more software-defined environments.
- Image management. Ideally, this team has separate duties to build and maintain a repository of container and workload images. Developers use these images in the pipelines intended for cloud deployment.
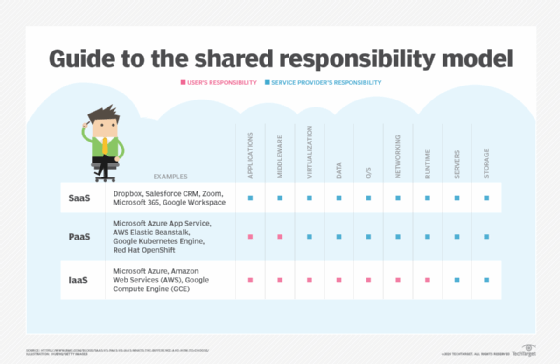
- IAM. Mature governance models include a separate IAM team that manages directory service integration, federation and single sign-on, as well as policy and role definitions within SaaS, PaaS and IaaS environments. If there isn't a distinct team, then at least commit a few IT operations or DevOps engineers to focus on this.
- Information security. All teams should incorporate infosec to integrate scanning tools and standards for acceptable code, system and image vulnerabilities, pipeline monitoring and secrets management. They should also define and maintain standard definitions for network security parameters and tools.
To ensure cohesion across teams, form a cloud governance committee with representatives from all these areas, as well as dotted-line representation from legal, compliance, audit and technology leadership. Once a central cloud governance structure is in place, there are still some important steps to take.
1. Establish security standards and baselines
Develop baseline security standards in collaboration with the governance team. At a minimum, the list should include cloud control plane configuration, IaC templates, cloud workload vulnerability posture, and assignment of DevOps and cloud infrastructure privileges.
2. Create a dedicated IAM function
Identities and role or privilege assignment are critical in the cloud, so dedicate an operational focus to this area.
3. Require multifactor authentication for all administrative access
Enable multifactor authentication for any privileged access to the cloud environment. This will help mitigate common brute-force attacks against administrative accounts.
4. Enable cloud-wide logging
All major cloud service providers offer logging services, such as AWS CloudTrail and Azure Monitor. Turn these on and send the logs to a centralized collector or service for analysis. Use logs to develop cloud behavior baselines and detect security events or incidents.
5. Invest in a cloud security posture management service
Organizations should continuously monitor everything from the cloud control plane to the current configurations of assets. As cloud deployments increase in number and complexity, a service that tracks configuration settings across numerous clouds or cloud accounts becomes invaluable to help detect misconfigurations that could cause security issues.
Cloud security vs. on-premises security
There are three significant differences between cloud security and on-premises security: shared responsibility, software and governance.
Shared responsibility
The concept of the shared responsibility model for data protection and cybersecurity has been part of most outsourcing arrangements for many years, but the nature of shared security responsibilities changed with the advent of cloud. Every major cloud provider supports shared responsibility in the cloud, but not all of these models are equal. For example, your IaaS cloud provider agreement should clearly delineate the responsibilities. AWS breaks down its responsibility model into two primary categories:
- Security in the cloud is the customer's responsibility. This includes data protection, IAM, OS configuration, network security and encryption.
- Security of the cloud is AWS' responsibility. This means the underlying pieces of the infrastructure, including the compute elements, hypervisors, storage infrastructure, databases and networking.
All cloud providers are wholly responsible for the physical security of their data centers. Additionally, they are responsible for data center disaster recovery planning, business continuity, and legal and personnel requirements that pertain to the security of their operating environments.
Cloud customers still need to plan for their own disaster recovery and continuity processes, particularly in IaaS clouds where they build infrastructure. Customers that want to manage data backups in SaaS and PaaS environments should incorporate these into existing data protection and recovery strategies.
Software
Another major difference between on-premises and cloud security is that everything in the cloud is software-based. This brings unique requirements for controls and processes, and potentially new tools and services to fulfill security objectives. Again, the cloud provider is responsible for managing and securing the hardware that underpins its services.
Governance
Be prepared to restructure governance workflows and alignments. In the cloud, they need to be much more agile and continuous, with representation from diverse groups of stakeholders and technical disciplines. You will need to involve a wider variety of stakeholders to make decisions much more quickly than is typical for on-premises governance practices.
Dave Shackleford is founder and principal consultant at Voodoo Security, as well as a SANS analyst, instructor and course author, and GIAC technical director.







